 cyberrisk governance system®
cyberrisk governance system®
Turning Cybersecurity into a Strategic Business Advantage
What is Cyber Risk Governance?
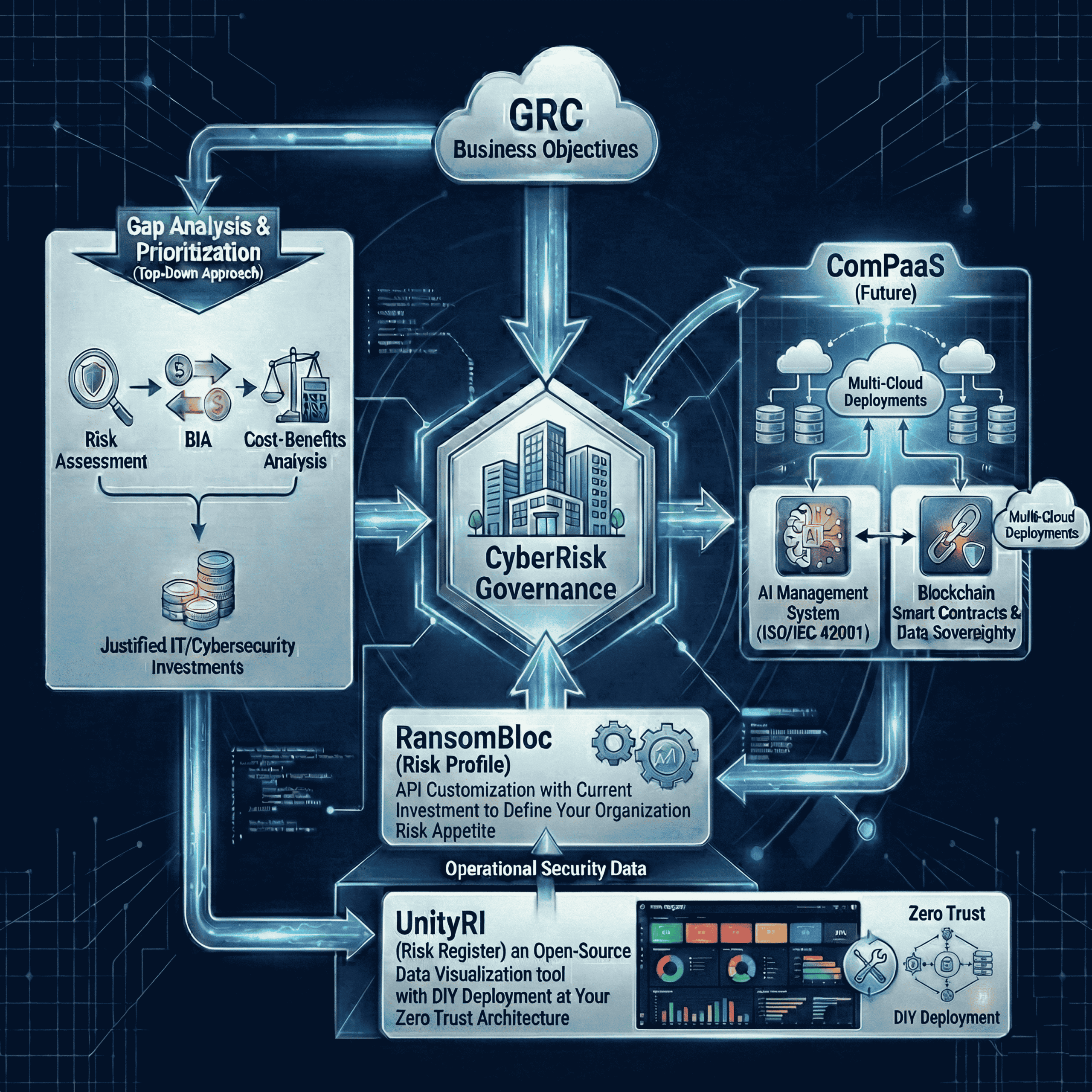
Cyber risk governance is the socio-technical discipline that bridges the gap between an organization’s cybersecurity operations and its enterprise governance obligations.
It establishes the structures, policies, and processes to identify, assess, quantify, and manage the risks associated with digital assets, data, and technology-dependent operations – translating technical security data into the financial, regulatory, and strategic language that three distinct stakeholder groups require:
- Business Executives accountable for fiduciary oversight and return on investment;
- Governors responsible for regulatory compliance, risk management, and audit readiness; and
- Technologists executing security operations and incident resolution.
Effective cyber risk governance aligns cybersecurity activities with business objectives, regulatory requirements, and stakeholder expectations – ensuring that cyber-related decisions are made consistently, transparently, and with measurable outcomes communicated through data visualization that all stakeholders can interpret and act upon.
 server room to board room
server room to board room
Protecting Revenue, Reducing Liability, and Demonstrating Fiduciary Responsibility
Why Defensibility Replaced Security
In the post-SEC Cyber Rule era, defensibility-not security-has become the board-level mandate. Organizations must demonstrate legally admissible evidence, quantified risk in dollar terms, and transparent accountability. Regulatory enforcement actions and breaches like Equifax and SolarWinds proved that documentation gaps transform operational failures into legal exposure.
Bridging the Server Room-Board Room Gap
Security teams speak in vulnerabilities and CVSS scores; executives require ROI, quantified risk, and compliance attestation. Compliance Tethering translates technical metrics like MTTD and MTTR into executive KPIs, enabling faster decisions and reducing board preparation time by 24%.
How Defensibility Creates ROI
Defensibility ROI manifests across four dimensions aligned with our CRG Cost Justification framework:
- Revenue Generation: Enables market access and customer trust
- Revenue Impact: Faster incident resolution minimizes disruption
- Efficiency Generation: Automation eliminates redundant compliance work
- Efficiency Impact: Workforce development reduces consultant dependency
The 5Cs Multiplier Effect
Defensibility compounds when the 5Cs Methodology operates in concert:
- Communication: Risk quantified for every stakeholder
- Collaboration: Eliminates silos and priority conflicts
- Customization: Adapts to any regulatory stack
- Customer: Extends accountability across the ecosystem
- Community: Institutionalizes cyber capability through workforce development
From Cost Center to Strategic Asset
The 3 Steps to C.A.R.E. framework operationalizes defensibility as a continuous process-establishing baseline evidence, prioritizing remediation by quantified risk, and maintaining ongoing documentation that withstands regulatory and legal scrutiny.
 sara service tiers
sara service tiers
SARA Comparison Strip
SARA Open-Source
-
Risk visualization
-
compliance mapping
-
exportable risk register
SARA Catalyst
-
API integration
-
vuln scanning
-
incident detection
-
ransomware disruption
-
immutable DB
SARA Pro
-
Resilience Index
-
audit readiness
-
board reporting
-
SME consulting
SARA Enterprise
-
AI² SLMs
-
InterOps Accelerator
-
Smart Contracts
-
ISO 42001 HitL
 cyberrisk governance methodology
cyberrisk governance methodology
Purpose-Built Modules Delivering Measurable Cyber Resilience
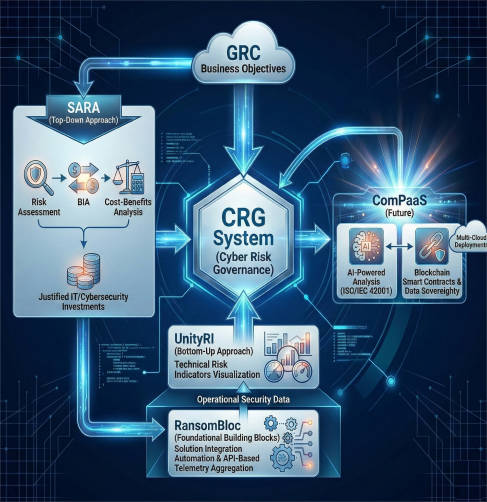
SARA – Security Automation & Risk Assessment – is the platform family that operationalizes the CRG methodology into a progressive product architecture. Each module is designed around a customer value ladder: reducing friction at entry, building depth through data accumulation, and creating natural expansion triggers as your risk governance maturity grows.
The SARA journey begins with SARA Open-Source, a free, self-service risk visualization tool that establishes your organization’s risk baseline and compliance posture – the essential first step before automation or expert assessment.
From that foundation, the SARA name defines the two core phases of the CRG methodology in practice:
SA – Security Automation is delivered through SARA Catalyst: integrating your existing systems, automating data collection, and building the holistic risk picture that connects boardroom governance objectives with operational security telemetry.
RA – Risk Assessment is delivered through SARA Pro: where Subject Matter Experts interpret the automated data foundation that Catalyst built, transforming raw security intelligence into quantified, board-presentable risk governance outcomes.
Coming soon: SARA Enterprise with AI² – the autonomous tier, extending the CRG methodology with artificial intelligence capabilities for organizations ready to operate at machine speed with human governance oversight.
Awareness first. Automation second. Expert assessment third. Autonomous governance ahead.
SARA Open-Source – DIY
Risk Governance Visualization for Executive Decision-Making (Self-Service)
SARA Open-Source is a single-pane-of-glass risk visualization platform that aggregates technical security data from cybersecurity systems, governance controls, and technical controls benchmarks into a unified, board-presentable view.
Built on our patented CRG methodology (USPTO #11,870,812), it transforms fragmented security telemetry into quantified risk indicators that executives, governance teams, and technologists can collaborate and act on — eliminating the communication gap that produces inaction paralysis.
Key Capabilities

SARA Catalyst - Security Automation
Integrate Your Existing Systems. Automate Your Risk Visibility.
SARA Catalyst is the Security Automation engine of the CRG platform – designed to protect and extend your existing technology investment, not replace it. Through API-based integration with your current security infrastructure, SARA Catalyst connects bottom-up system telemetry to top-down governance objectives, delivering a holistic risk trending analysis that no single tool in your stack provides alone.
Your organization has already invested in vulnerability scanners, SIEM platforms, and log collectors. SARA Catalyst unifies these data sources – whether open-source solutions like OpenVAS, Wazuh, and Zeek, or commercial platforms already in your environment – into a single automated data stream hosted on an immutable database architecture, ensuring data integrity and audit-ready traceability.
Key Capabilities

SARA Pro - Risk Assessment
Expert-Led Risk Governance. Board-Ready Outcomes.
SARA Pro is the Risk Assessment layer of the CRG platform – where Subject Matter Experts transform the automated data foundation built by SARA Catalyst into quantified, actionable risk governance outcomes. Delivered as “SARA with Subject Matter Expertise,” SARA Pro enables independent cyber risk consultants, compliance advisors, and specialized certifiers to deliver enterprise-grade risk governance under their own brand, backed by data analytics.
Where SARA Catalyst answers “what is happening in our environment,” SARA Pro answers “what does it mean, and what should the board do about it.”
Key Capabilities
SARA Enterprise with AI² - Autonomous Governance
From Detection to Self-Healing. From Reactive to Autonomous.
SARA Enterprise represents the autonomous evolution of the CRG methodology – where the Security Automation foundation built by SARA Catalyst and the Risk Assessment intelligence refined by SARA Pro converge with domain-specific artificial intelligence to deliver cyber resilience that operates at machine speed under human governance oversight.
At the core of SARA Enterprise is AI² – CRG System’s AI architecture that feeds organizational data into organization-specific models with reinforcement learning. The InterOps Accelerator (iA), under USPTO Patent #11,870,812, serves as the autonomous execution engine – handling threat correlation, automated remediation workflows, and compliance verification.
SARA Enterprise does not replace human judgment. It operates autonomously within pre-defined policy boundaries established by organizational stakeholders; exceptions escalate to human oversight.

Who We Are
33 years of experience. Meet the leadership and 12-member advisory board.
Who We Serve
Six industry verticals, one governance framework.
Insights
5Cs Framework, partner research, LinkedIn Live events.
Contact Us
Free baseline assessment. Five deliverables in 7 days.
 get started
get started
See What CRG Can Do For Your Organization
Start with a free baseline assessment – five deliverables in seven days. No commitment, no vendor lock-in.




