 who we serve
who we serve
Cyber Risk Governance for Growing SMBs
Cybercriminals target SMBs precisely because 73% lack confidence their current solutions can protect them, and 60% of breached small businesses close within six months. The average data breach costs SMBs $254,000 — devastating for organizations allocating just 5–20% of IT budgets to security.
Enterprise security tools dominate the $95 billion security software market, engineered for organizations with dedicated security operations centers and multi-million dollar budgets. Meanwhile, 99.9% of businesses are SMBs operating with shared IT and security responsibilities, creating a fundamental market mismatch.
We don't sell you another enterprise tool with an SMB price tag. Our patented CyberRisk Governance (CRG) platform provides the infrastructure that makes enterprise-grade cyber risk management operationally achievable and economically viable for organizations with 50 to 5,000 employees.
 our difference
our difference
3 Things We Do Differently
We work with what you have.
No rip-and-replace. No forced upgrades. We integrate with your existing tools and make them work better together within a governance framework that connects technical controls to business outcomes.
We speak your language.
No jargon. No acronyms that require translation. We explain security in terms you can take to your board: risk, cost, and return on investment.
We meet you where you are.
Need to do it yourself? SARA Open-Source is free. Want guidance and support? SARA Catalyst walks you through it. Need hands-on expertise? SARA with Subject Matter Expertise delivers the work.
 industry overview
industry overview
Industries We Serve
We serve six primary industries where regulatory pressure, breach exposure, and budget constraints create the strongest demand for governance-led cybersecurity. Each vertical has unique regulatory requirements, and we tailor the CRG methodology to match.
FinTech & Financial Services
Managing cyber risk while meeting strict regulatory and compliance demands across digital lending, payments, and financial technology.
Healthcare
Protecting patient data while ensuring operational continuity and regulatory alignment across clinical and administrative systems.
Manufacturing
Reducing operational downtime and cyber exposure across converged IT and OT environments.
Hospitality
Securing distributed systems while protecting customer trust and brand reputation across properties.
Education
Safeguarding student records, research data, and staff information within tight budget constraints.
Non-Profits
Protecting donor data and meeting grant compliance requirements without diverting resources from your mission.
FinTech & Financial Services
Cyber Risk Governance for Regulated Financial Organizations
THE PROBLEM
You handle millions in transactions daily. One breach costs $6.08 million on average in the financial services sector. Regulators demand proof you’re protecting customer data. Cyber insurance is nearly impossible to get – over 40% of claims get denied for missing documentation.
The pressure is especially acute for digital lending platforms and FinTech organizations operating under multiple regulatory frameworks simultaneously. Among US digital lending platforms, 93% admit to having problems meeting regulatory requirements. In 2023, NYDFS fined BitFlyer USA $1.2 million specifically for failing to perform adequate risk assessments – a FinTech with a staff profile consistent with the organizations we serve.

Healthcare
Protecting Patient Data While Enabling Operational Continuity
THE PROBLEM
Healthcare breaches cost $10.22 million on average – more than any other industry, for 14 years running. HIPAA fines have increased 340% in the last year. Detection takes 279 days on average – the longest of any industry.
Patient data leaks destroy trust and create legal exposure that extends well beyond the breach event itself. Clinical organizations face the additional challenge of securing medical devices and cloud-based care management platforms where patient data moves through every step of the clinical path.
WHAT WE DO
SARA Catalyst identifies threats with AI-driven analysis to reduce false alarms, enabling your team to prioritize indicators of compromise that relate directly to your compliance objectives. SARA scans your environment and shows exactly where your cyber risk gaps are, detecting zero-day and signature-less infections before breach.
Every finding maps directly to HIPAA, HITECH, and FDA regulatory requirements – not just a threat list, but a governance-ready compliance picture.
Manufacturing
Managing Cyber Risk Across IT and Operational Technology
THE PROBLEM
Manufacturing is the number one target for ransomware – 87% increase in attacks last year. One hour of downtime costs $125,000. Seventy-five percent of OT attacks begin as IT breaches. Your IT team is already stretched thin managing production systems.
The convergence of IT and operational technology environments creates a uniquely dangerous attack surface where a network vulnerability can shut down physical production lines.
WHAT WE DO
We connect your technical resources to your compliance requirements. When we find gaps, we show you exactly what to fix first – no guessing. SARA gets you ISO 27001 and NIST CSF ready with your current technology investment, supported by Subject Matter Experts who provide cost efficiency and operational effectiveness.
Hospitality
Securing Distributed Operations and Customer Trust
THE PROBLEM
You store thousands of guest records and credit cards. PCI DSS compliance is mandatory. One breach like MGM’s costs $30 million and destroys your reputation. Eighty-nine percent of hospitality businesses that get breached get breached again. Insurance companies will not cover you unless you prove continuous security.
WHAT WE DO
We monitor every device, reservation system, and guest Wi-Fi network. The Unity Risk Indicator shows your cyber risk status in real time, not once a year. SARA finds optimal resolution paths that balance technical and compliance priorities, providing data analysis as risk profiles for executives and supply chain partners to make decisions based on their roles and responsibilities.

Education
Safeguarding Student Data Within Tight Budgets
THE PROBLEM
Student records, parent data, financial aid information, research data, and staff payroll – all attractive targets. Budget cuts mean your IT team is already doing three jobs. Data breaches trigger mandatory reporting and legal exposure.
Educational institutions are increasingly targeted because they hold large volumes of personally identifiable information while typically operating with minimal dedicated security staff.
WHAT WE DO
We secure your network without requiring additional specialized security staff. The Unity Risk Indicator gives administrators a holistic dashboard that transforms cybersecurity into a data analytics journey of cyber risk management – visual, understandable, and actionable.
SARA helps you meet FERPA requirements without hiring expensive consultants, providing compliance and risk expertise through a subscription service structure that fits education budgets.
Source: Who_We_Serve_Hybrid.docx education section. FERPA requirements: US Department of Education.

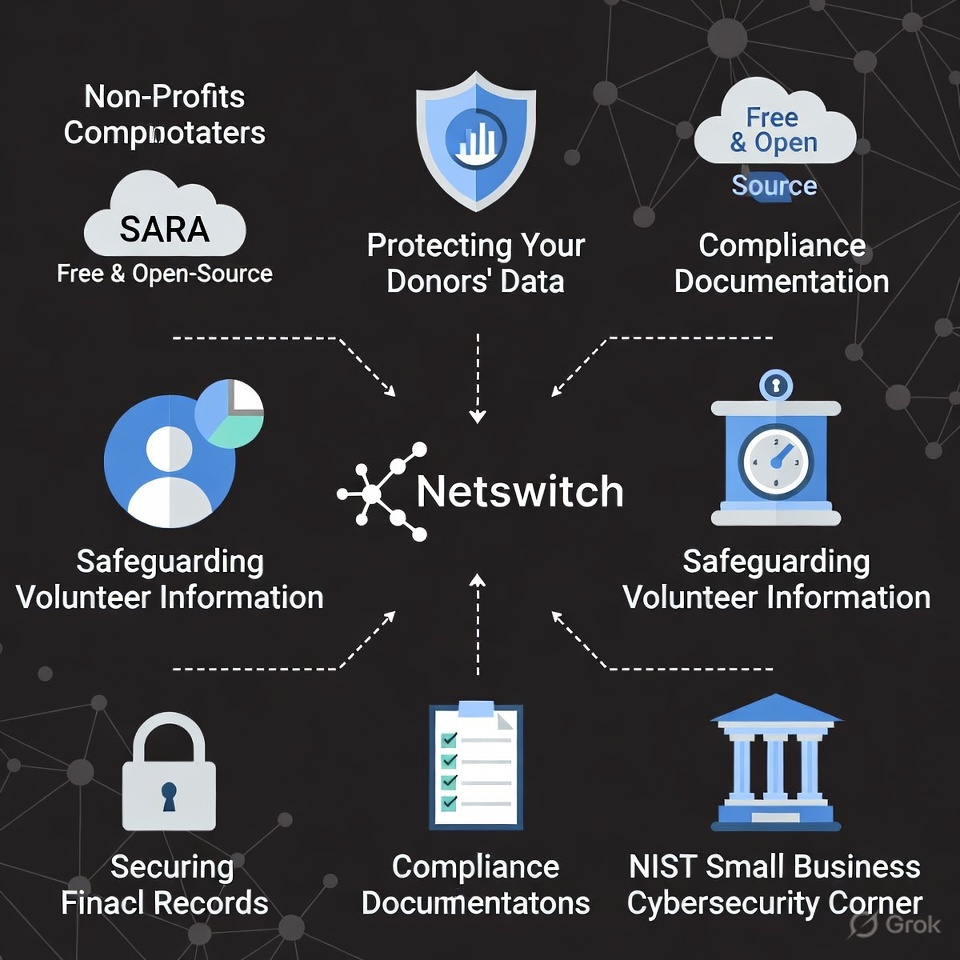
Non-Profits
Enterprise Protection Without Diverting From Your Mission
THE PROBLEM
Donor data, volunteer information, and financial records need protection – but your budget goes to your mission, not IT security. One breach erodes donor trust and threatens your nonprofit status. You cannot afford dedicated security staff.
WHAT WE DO
We provide enterprise-level security at investment levels non-profits can sustain. SARA Open-Source is free and open-source – giving you immediate protection for donor data with zero financial commitment. When you need more, our platform scales with flexible options designed for mission-driven organizations.
No-cost tools let you start protecting donor data today. Compliance documentation for your board and grant requirements. All without breaking your budget or diverting resources from your mission.
Source: Who_We_Serve_Hybrid.docx non-profits section. Non-profit cybersecurity guidance: NIST Small Business Cybersecurity Corner.
 challenges we solve
challenges we solve
Challenges We Hear Every Day
“We can’t get cyber insurance.”
Fifty percent of small and mid-sized businesses get denied coverage. We provide the documented controls and continuous monitoring insurers require. Several clients reduced premiums after implementing our platform.
“We failed our audit.”
SARA finds compliance gaps before auditors do. We give you a prioritized list of what to fix and help you fix it. One client went from 26% to 100% compliance in 6 months.
“We don’t have a security team.”
Neither do most of our clients. SARA Catalyst automates threat blocking 24/7. The Unity Risk Indicator gives executive visibility without requiring security expertise. You do not need to hire a CISO to be secure.
“Our board asks if we’re secure and we don’t know how to answer.”
The Unity Risk Indicator translates technical security into plain language. Green means good. Yellow means needs attention. Red means fix now. Your board gets it immediately.
 the numbers that matter
the numbers that matter
Average Breach Cost by Industry
| Industry | Average Breach Cost (US$) |
|---|---|
| Financial Services | $6.08 million |
| Healthcare | $10.22 million |
| Manufacturing | $5.56 million |
| Hospitality | $4.03 million |
| SMB Average | $254,000 |
Additional Risk Factors
- Over 40% of cyber insurance claims denied for missing documentation
- Only 10% of SMBs have cyber insurance vs. 80% of large enterprises
- 68% of CISOs not ready for SEC’s 4-day breach disclosure timeline
- 60% of breached small businesses close within 6 months
Source: IBM Cost of a Data Breach Report 2024. Fitch Ratings Cyber Insurance Analysis 2024. Verizon DBIR 2024. Risk.net Operational Risk Survey 2023. Woodruff Sawyer Cyber Insurance Market Analysis 2025.
Not Sure Where to Start?
Complete our free security risk assessment – you keep the results to yourself until you’re ready to share them with us. You’ll receive:
- Business Impact Analysis Playbook and Workbook
- Open-source Data Visualization Tool (SARA Open-Source)
- Human Risk Management Assessment
- Information Security & Risk Outlook Self-Assessment
- Cybersecurity Insurance Requirements Checklist












